Say, you want to test your anti-virus program on your PC. Using real viruses for testing in the real world is rather like setting fire to the dustbin in your office to see whether the smoke detector is working. Such a test will give meaningful results, but with unappealing, unacceptable risks.
Since it is unacceptable for you to send out real viruses for test or demonstration purposes, you need a file that can safely be passed around and which is obviously non-viral, but which your anti-virus software will react to as if it were a virus.
The good news is that such a test file already exists. A number of anti-virus researchers have already worked together to produce a file that their (and many other) products "detect" as if it were a virus.
It's called EICAR.COM anti malware testfile. It is also short and simple - in fact, it consists entirely of printable ASCII characters, so that it can easily be created with a regular text editor.
So, without any further ado, lets get down to brass tacks.
Step 1: Open Notepad.
Step 2: Type this string without quotes:
Since it is unacceptable for you to send out real viruses for test or demonstration purposes, you need a file that can safely be passed around and which is obviously non-viral, but which your anti-virus software will react to as if it were a virus.
The good news is that such a test file already exists. A number of anti-virus researchers have already worked together to produce a file that their (and many other) products "detect" as if it were a virus.
It's called EICAR.COM anti malware testfile. It is also short and simple - in fact, it consists entirely of printable ASCII characters, so that it can easily be created with a regular text editor.
So, without any further ado, lets get down to brass tacks.
Step 1: Open Notepad.
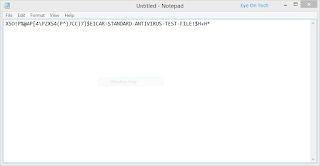
Step 2: Type this string without quotes:
"X5O!P%@AP[4\PZX54(P^)7CC)7}$EICAR-STANDARD-ANTIVIRUS-TEST-FILE!$H+H*"
Step 3: Save it as "eicar.com" (crucial to save it with .com extention).
Now you will see the testfile detected by your antivirus program as malicious.
If not detected, your anti-virus is not working. That's all.


Comments
Post a Comment